Architecture
Traversal BYOC is deployed, fully-managed, and operated by Traversal inside of a separate, dedicated cloud account that you own; for example, a separate AWS account part of your AWS organization. This separation helps protect the security of your systems and applications while providing Traversal with the access necessary to deliver and maintain a highly-available service.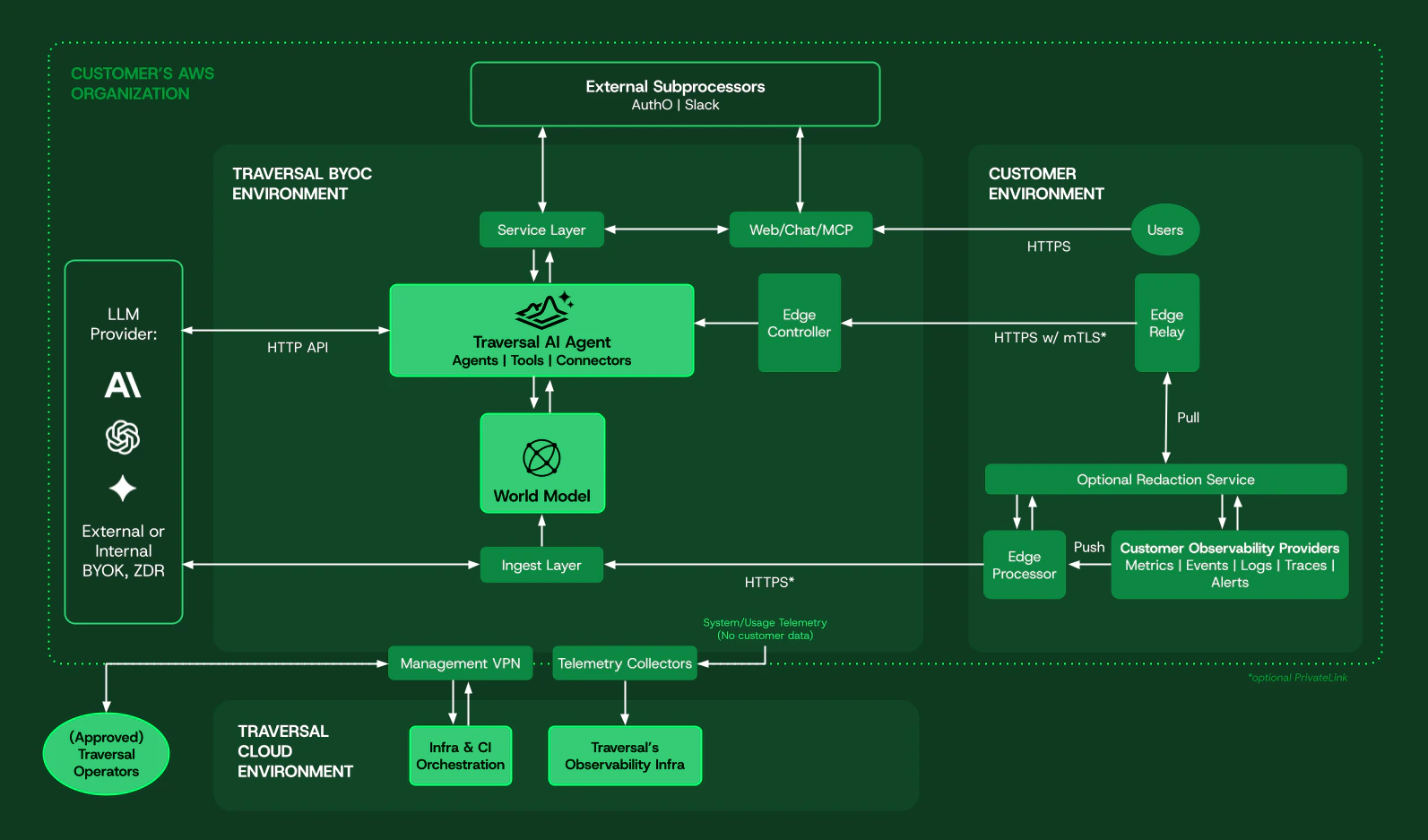
Traversal’s web application and authentication are currently handled by external providers outside of the BYOC deployment. A private deployment option for those services will be available in the future.
Networking
The entirety of the Traversal BYOC environment is deployed in a dedicated VPC, with all relevant infrastructure spread across multiple availability zones and hosted in private subnets. Traversal requires a minimum of three/20 private CIDR range subnets (one per availability zone) for its deployment and operations.
Compute
All compute powering Traversal’s services, data stores, data pipelines, agentic workflows, and applications, runs on cloud instances (in AWS, EKS-on-EC2) and managed cloud services inside of the provided, dedicated cloud account.AI Models and Inference
Traversal uses frontier AI models (LLMs) to power its AI SRE agent. At your discretion, those models can be cloud-hosted (from LLM providers directly, with or without BYOK), routed through a private gateway, or fully hosted in your cloud environment (in AWS, with Bedrock).Access control
Access to your BYOC deployment of Traversal by your users is always secured and controlled by Single Sign-on (SSO) with your Identity Provider. Access by Traversal operators for maintenance and support is made through a secure and audited Tailscale-based VPN, restricted to authorized Traversal personnel only, and always secured by SSO with second-factor authentication.Telemetry
By default, system telemetry used to monitor your BYOC deployment of Traversal is sent to Traversal’s observability solution outside of your environment. If needed, some telemetry attributes can be redacted or filtered before leaving your BYOC deployment. Usage data (for billing purposes) is also sent to Traversal’s usage metering solution outside of your environment. All telemetry data is always sent securely over HTTPS to authenticated endpoints.Data security
All data stored by Traversal in databases, network-attached storage volumes, and cloud storage buckets remains in your AWS account dedicated for Traversal’s BYOC deployment. Data is always encrypted at rest and in-transit by best-in-class encryption from your cloud provider (AES-256 and TLS1.3).Network security
Within the Traversal platform, all service-to-service traffic is authenticated and encrypted in-transit with mTLS/TLS1.3. Connections to your private data sources and environments are always made through dedicated, private, secure, and encrypted network paths (PrivateLink) with Traversal’s Edge Relay.Ingress
By default, no inbound connections to your Traversal BYOC deployment can be made from the public internet. Your access and connection to Traversal is routed through your private network. The following inbound connections (through secure PrivateLink service endpoints) must be established and allowed:- From your users to Traversal’s web application and API;
- From your Edge Relay client to the Edge Controller in your Traversal BYOC deployment;
- If deployed, from your Edge Processor to your Traversal BYOC deployment’s data ingest endpoint.
https://api.<customer>.traversal.com/slack/*.
Egress
To ensure the proper operation of your Traversal BYOC deployment, the following outbound connections must be allowed:- To
login.traversal.comand*.auth0.comfor authentication; - To
telemetry.traversal.comfor reporting system telemetry and usage metering data to Traversal; - To
*.pagerduty.comfor monitoring and alerting; - To
*.tailscale.comfor Traversal’s Tailscale-based operational VPN (required for upgrades, maintenance, and support); - To
okta.comfor authentication of Traversal operators with our identity provider; - To
letsencrypt.orgfor issuance of SSL/TLS certificates; - If configuring integrations with any third-party vendor, to their endpoint domains:
- To
*.slack.comfor the Traversal Slack app - To
github.comto access your source code repositories - To
api.anthropic.comand/orapi.openai.comfor access to our LLM providers if you’re not using Bedrock
- To
- Your Traversal BYOC deployment at
<customer>.traversal.comandapi.<customer>.traversal.com; login.traversal.comand*.auth0.com;- Optionally, to our user telemetry data processors, Amplitude and Sentry.
Deployment
To deploy Traversal BYOC, after establishing your agreement with Traversal and reviewing the responsibility matrix below, you must:Provision a new, dedicated AWS account attached to your organization, specifically for use by and for Traversal.
Deploy the Traversal BYOC AWS CloudFormation Template into this account to initialize a provisioning IAM role used by Traversal for deployment and operations.
https://<customer>.traversal.com. Following this initial deployment, and depending on the needs of your environment, you will:
Deploy the Edge Relay to enable access to your private telemetry and data sources in your environment
Operations
Traversal BYOC deployments are fully managed and operated by Traversal, and providing the same high-availability guarantees as our SaaS offering. Experienced Traversal operators continuously monitor, tune, and deploy updates to your Traversal BYOC deployment to ensure the highest quality of service for Traversal users.Responsibility matrix
| Category | Component | Traversal | Customer |
|---|---|---|---|
| Infrastructure | Provision and initialize a dedicated cloud account | ||
| Management of compute and storage quotas | |||
| Networking | VPC and networking infrastructure in the BYOC account | ||
| PrivateLink / VPC Service Endpoints | |||
| Firewall | |||
| Security | Provisioning IAM role | ||
| Data encryption at rest and in transit | |||
| Secrets management | |||
| Application-level authentication and authorization | |||
| Data | Source data sovereignty and governance | ||
| Governance on Traversal indexed data | |||
| Backups and data retention | |||
| Software | Deploy the Traversal BYOC environment | ||
| Maintain and operate the Traversal BYOC environment | |||
| Deliver a highly-available Traversal experience | |||
| Configure users, roles, and data/service integrations | |||
| Use the deployed Traversal BYOC environment to investigate and resolve your incidents | |||
| Billing | Cloud account and infrastructure costs | ||
| Licensing costs of Traversal | |||
| Provide metering-based invoices for usage of Traversal |
