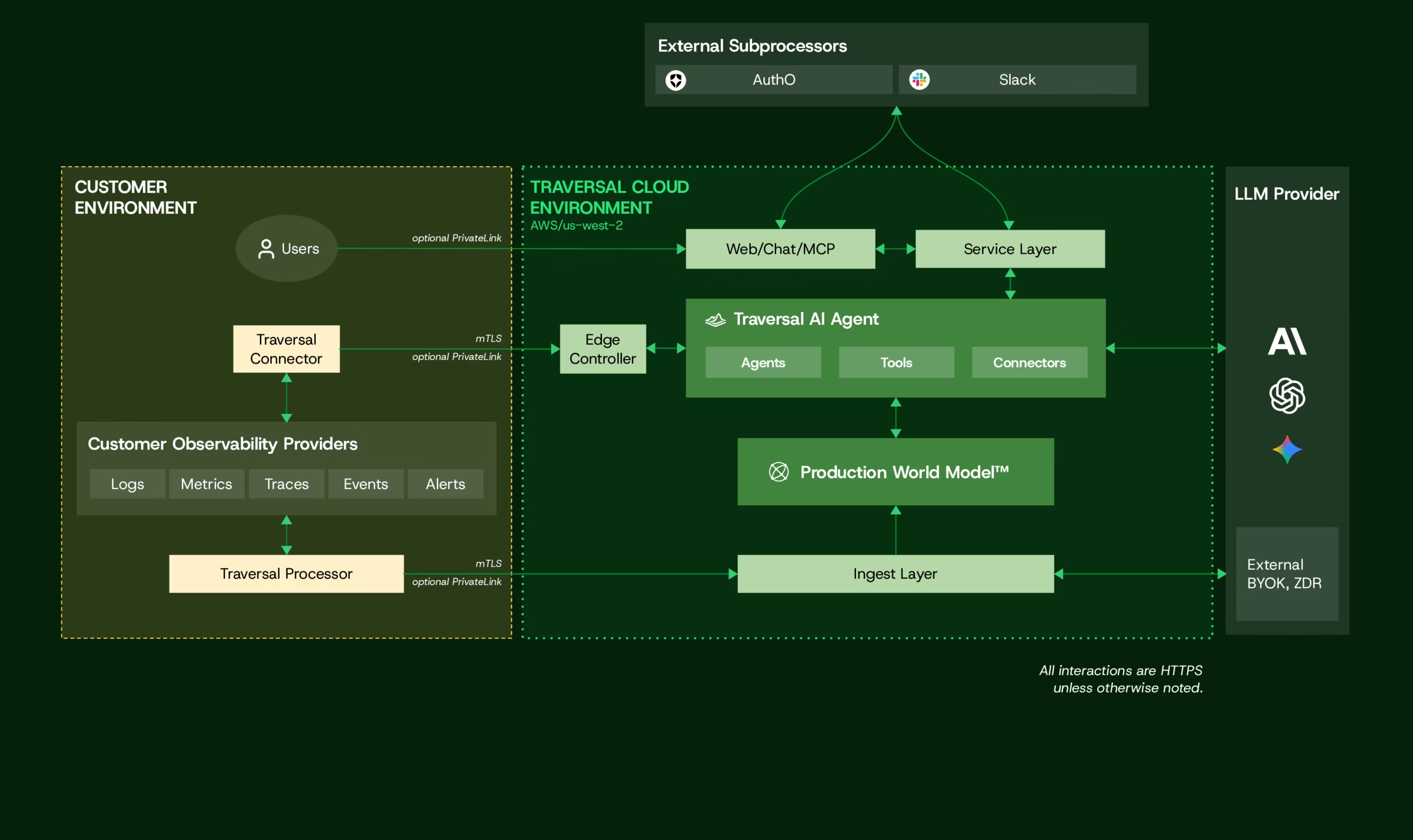
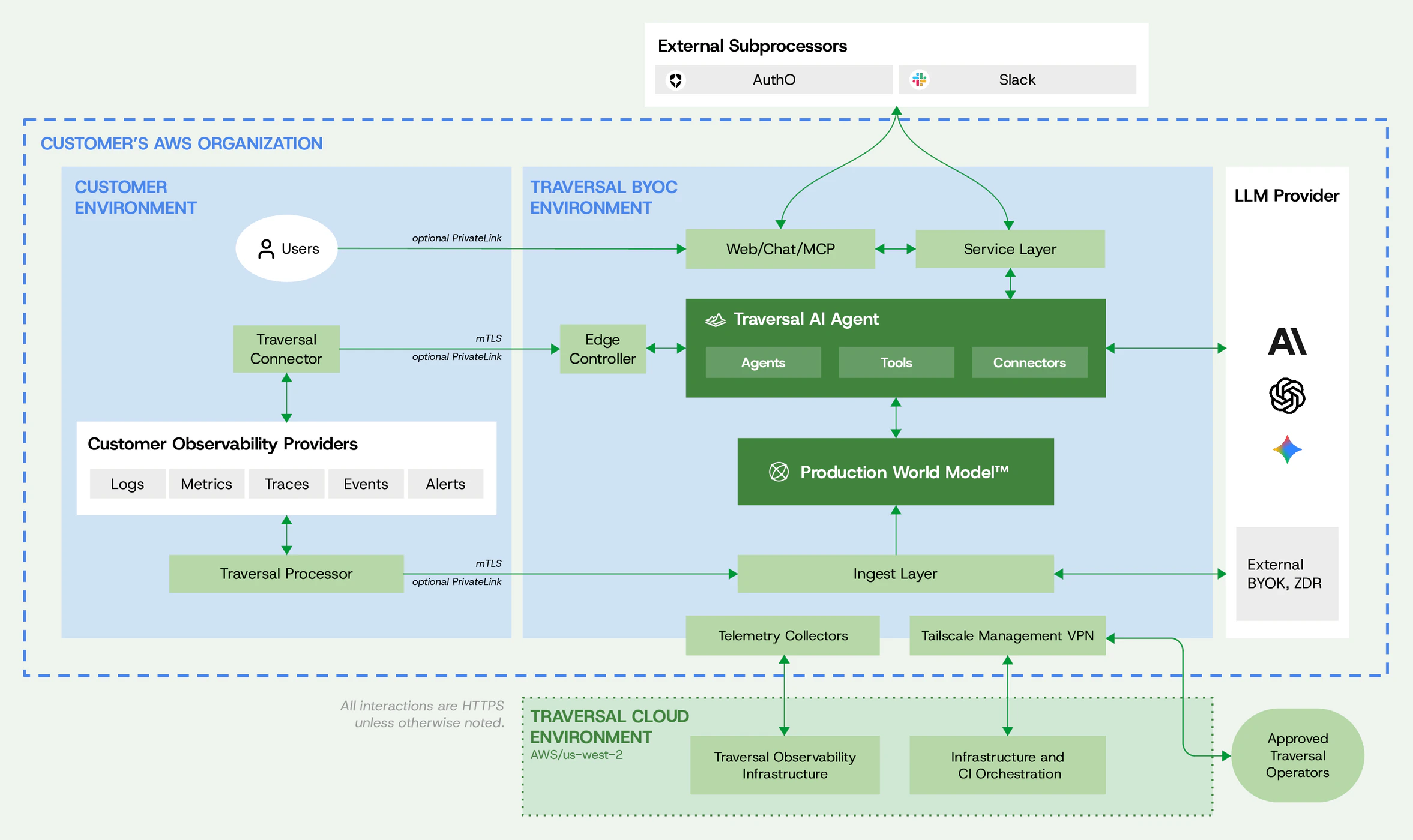
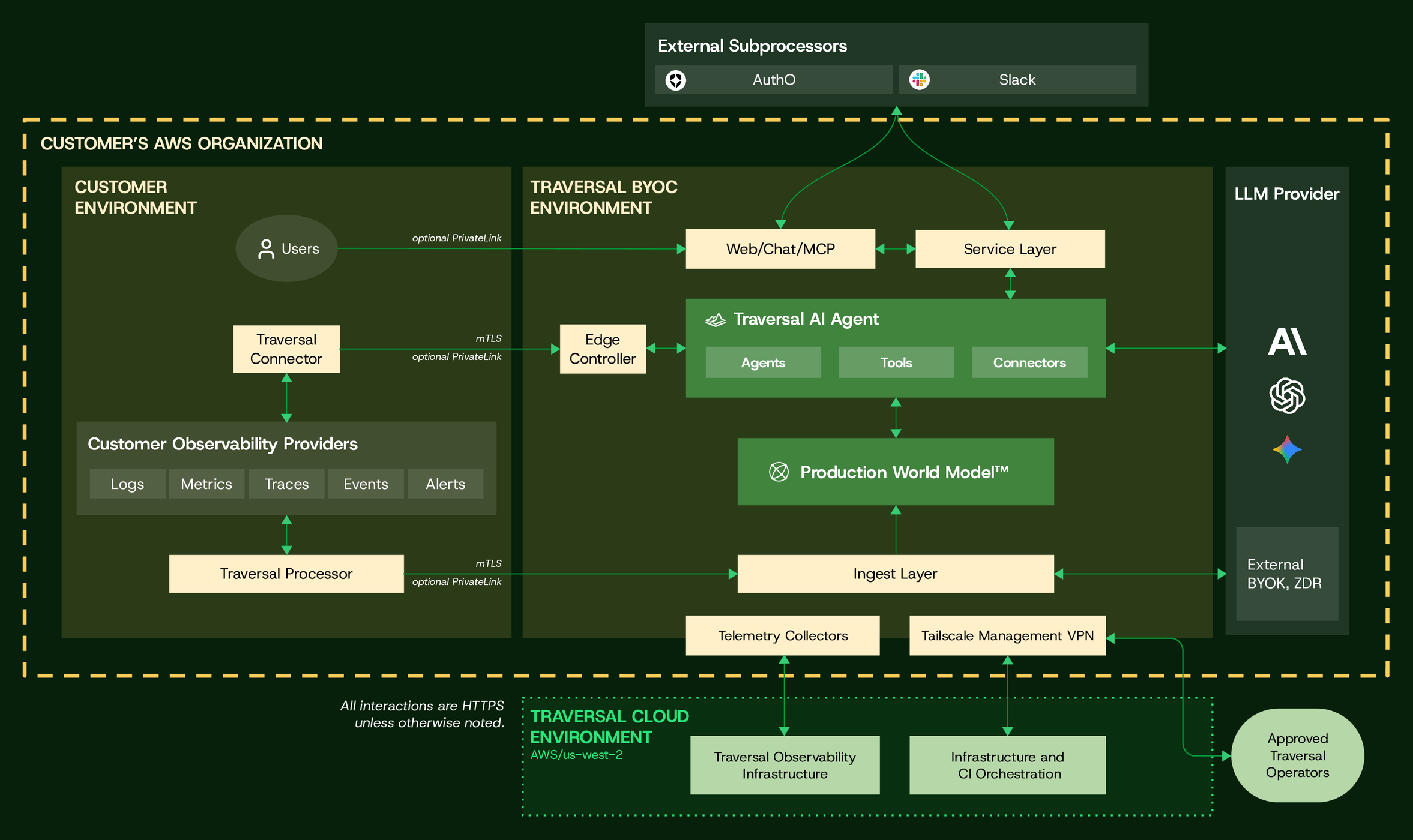
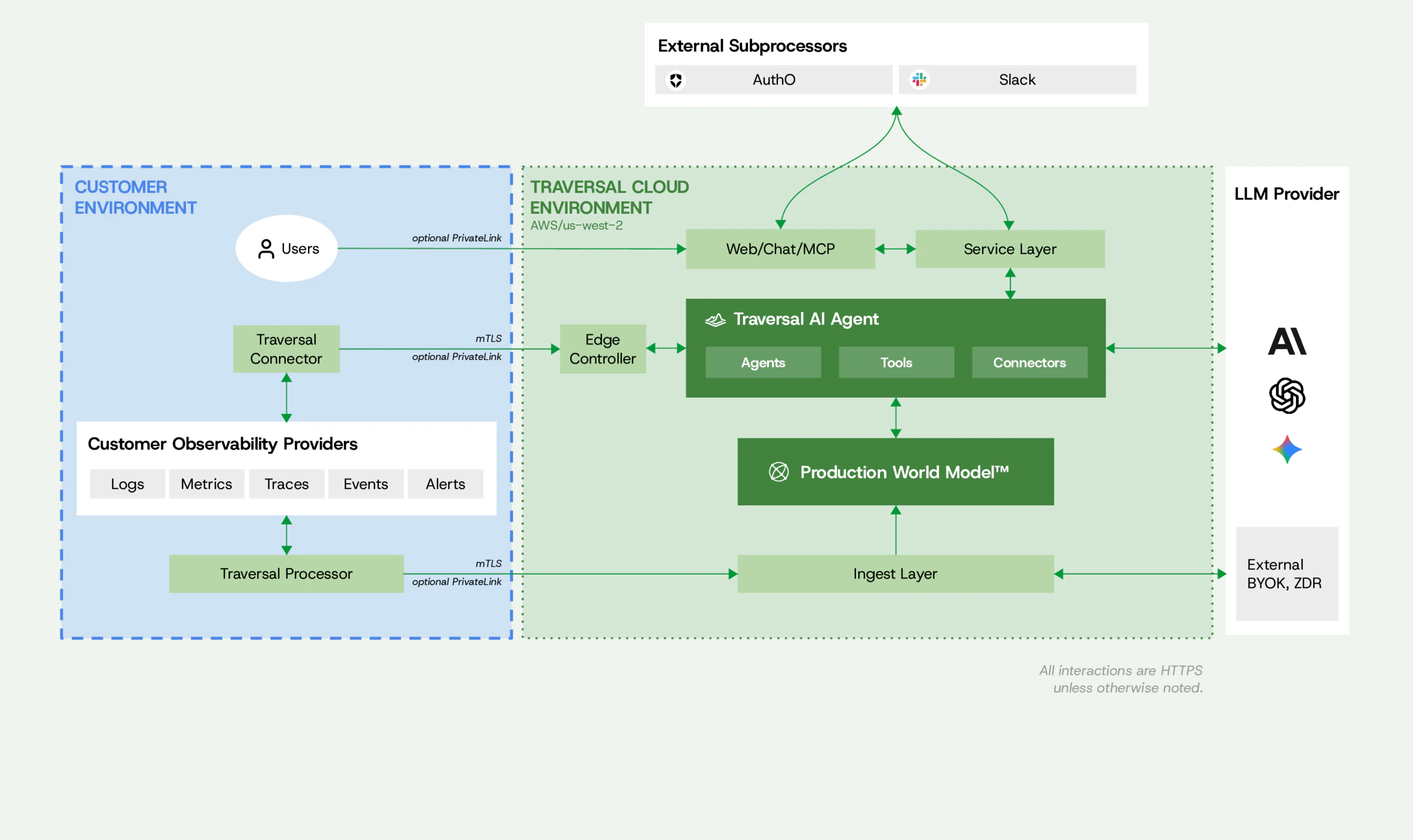
Traversal is agent-less and always read-only. In most cases, Traversal does not require the deployment of any software in your environment, and it cannot modify your systems or data. The Traversal Connector can be deployed to securely reach private data and observability sources, and the Traversal Processor can be deployed to minimize egress volumes and apply data redaction before data leaves your environment. Both the Traversal Connector and Traversal Processor run in any environment — AWS, GCP, Azure, OCI, on-prem Kubernetes, or any container runtime. Kubernetes is the easiest path: we publish Helm charts for both. Traversal offers two deployment options: SaaS to get going in minutes with Traversal’s cloud, or BYOC (Bring Your Own Cloud) for a dedicated, single-tenant, fully-managed deployment in your own cloud account.Documentation Index
Fetch the complete documentation index at: https://docs.traversal.com/llms.txt
Use this file to discover all available pages before exploring further.
SOC 2 Type II certified
Traversal has received and maintains its SOC 2 Type II attestation, applicable to both deployment options.
- SaaS
- BYOC (Bring Your Own Cloud)
The easiest way to get started in minutes with Traversal is by signing up on Traversal’s SaaS/cloud offering. Your data and connections to your observability providers remain fully secure, whether they are cloud vendors or you host them in your internal infrastructure.Communication from the Traversal Connector and Traversal Processor to the Traversal SaaS travels over the public internet and is secured with mTLS — both sides authenticate with certificates, and all traffic is encrypted in transit.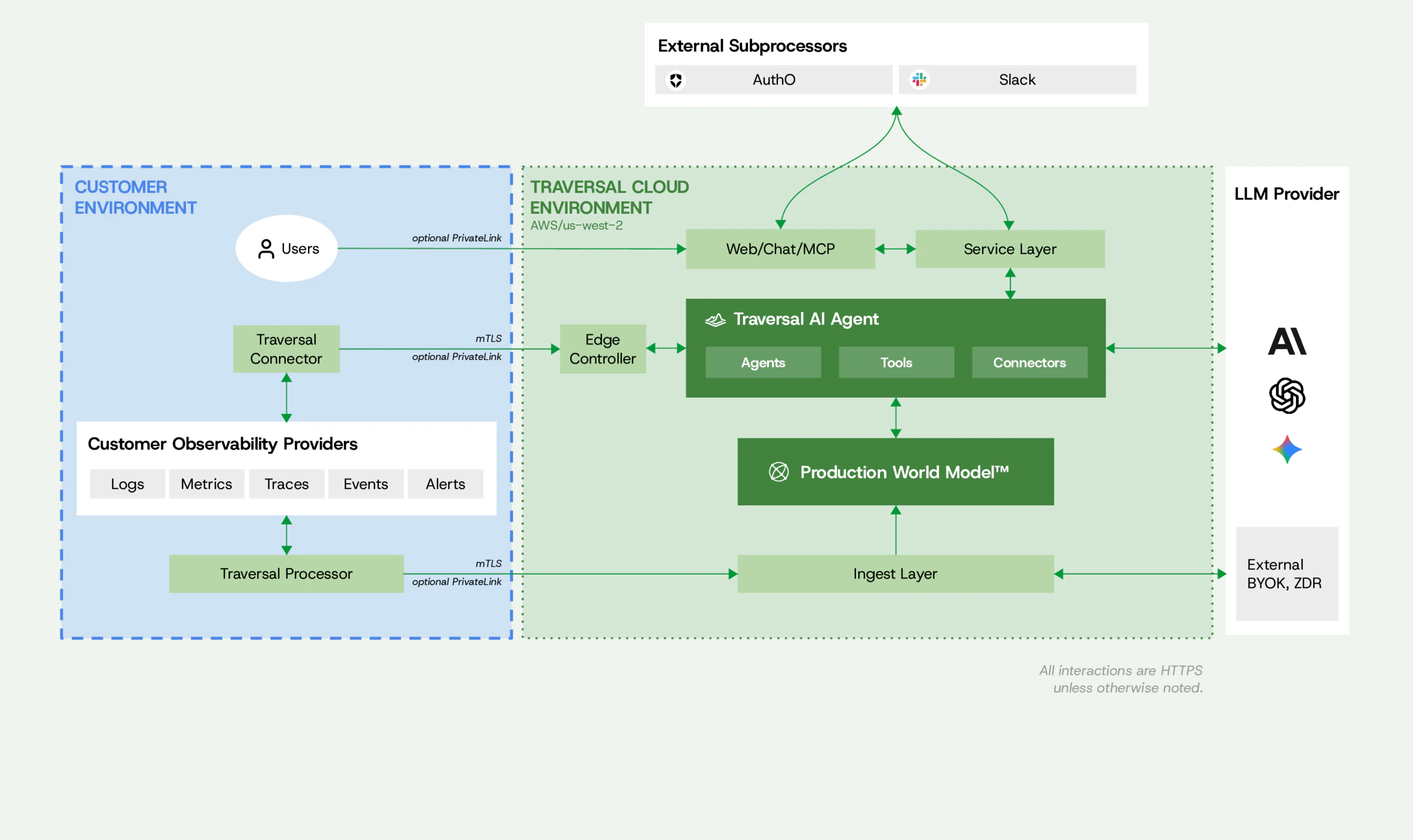
Tenant isolation
At every layer — from frontend to database and agentic workflows.
Zero data retention
On LLM calls, with options to bring your own key (BYOK) and bring your own provider.
Secure access
Connect to your private data sources and systems with the Traversal Connector.
Minimal egress
Reduce data leaving your environment with the Traversal Processor.
Data redaction
Customer-configured data redaction and obfuscation at the edge.
Strong authentication
SSO and MFA for all users.